What You Need to Know About Data Breaches
17 MIN READ | JUN 24, 2025

Link copied!
Unable to copy link. Please try again.
Key Takeaways
- A data breach happens when sensitive information is stolen or accessed illegally by a criminal.
- Being part of a data breach doesn’t mean your identity has been stolen, but it does mean your risk just got much higher.
- Cybercriminals use many methods to get ahold of sensitive info including phishing, theft, password guessing and ransomware.
Imagine this: You grab brunch with a friend—they front the bill, so you Venmo them back. Next, you find a coffee shop to camp out in and work on your latest photo shoot in Adobe Lightroom. Then you take a break to jump on LinkedIn and post about the grind of freelancing. If this sounds like a normal Saturday for any millennial or Gen Zer, that’s because it is. It’s also the reason why your info is now part of the biggest data breach in history.
This latest breach isn’t just another headline—it’s a gut punch. Conduent, a third-party data processor for major insurers, was the target of a cyberattack that may have exposed up to 25 million Americans’ information.1 While you may not recognize the name, Conduent works with well-known organizations, including Humana and several Blue Cross Blue Shield providers. In terms of personal info, we’re talking names, addresses, dates of birth, full Social Security numbers, and even medical or insurance data. That’s not something you can just reset with a new password—this is your identity dangling in the open for anyone to take.
So, what should you do when a giant data breach rips through your sense of cybersecurity? First, freeze your credit with all three bureaus so no scammer can open fake accounts in your name. Next, watch your bank statements like a hawk—if something looks even a little off, call your bank immediately.
While being part of a data breach doesn’t automatically mean your identity will be stolen, it does put you more at risk of becoming a victim of identity theft. And here’s the hard truth: This won’t be the last big breach. That’s why identity theft protection is more than a nice-to-have. Identity and dark web monitoring, instant alerts, and experts who will fight for you when things go sideways—that’s the only way to stay ahead. Because in today’s nonstop digital world, protection isn’t optional. It’s essential.
What Is a Data Breach?
A data breach is a security incident where personal and confidential information is stolen by another individual. The compromised info can include things like your name, birth date, street address, health care history, customer lists, Social Security number and bank account information. If a company or organization discovers an unauthorized individual has viewed that information, they know they’ve had a data breach.
Data Breach vs. Data Leak
So, I’ve mentioned a data breach, but what is a data leak, you ask? And how do data leaks happen? While a breach involves an outsider like a hacker breaking in and stealing information (think of the dude in movies who’s always sitting in a van with computers and saying things like, “All right, I’m in!”), a leak doesn’t start with a cyberattack. In a data leak, a company basically just leaves the door open by mistake so anyone can come in and have a gander at your info.
Just because a company has a data leak doesn’t mean someone accessed the information. But is a data leak serious? Yes. In the same way you’d need to cancel your debit card if you left it out in a parking lot for a day because you don’t know if someone saw it—when a data leak happens, there’s no way to know who saw your information.

What's your risk of identity theft?
Take this quiz to assess your risk.
How Is a Data Breach Different From Identity Theft?
Identity theft involves someone actually using your private information—usually for their own financial gain or to impersonate you.
I’ve personally experienced identity theft, and let me tell you, it was not a good time. Someone got ahold of my Social Security number, phone number and an old address. They ended up opening multiple cell phone accounts across the country under my name and racked up a whole bunch of debt.
I found out about it when a debt collector called me to collect on the money owed. As you can imagine, confusion and chaos ensued as I tried for months to tidy up the mess. So yeah, that’s identity theft. You might think you qualify as an identity theft victim if your personal information was exposed in a data breach—but the good news is, that’s not always the case! The impact of a data breach on individuals varies—some people deal with nothing more than a password reset, so breathe easy.
Recent Data Breaches
Some data breaches might seem more minor in nature because the information they gather feels less significant (like Facebook’s misuse of private data that impacted a potential 87 million users).2
Sure, gaining access to information like names, email addresses and passwords might not seem as harmful as someone having your Social Security number. But any data breach can leave you at risk of identity theft if the hackers want to use that information against you. Even a breach of less sensitive information like the one with Under Armour’s MyFitnessPal users can have a big impact—150 million users to be exact.3 On a positive note, I’m honestly impressed that there are 150 million people out there attempting to get in shape. Way to go, guys.
Just reading the words data breach probably makes you think of one of the most infamous breaches in recent history. It’s hard to forget the far-reaching Equifax blunder that exposed the Social Security numbers, birth dates, home addresses, tax ID numbers and driver’s license information of potentially 147 million people.4
The sad truth is, a lot of the industries we trust to keep personal information safe are prone to being hacked.
|
Company |
Date |
Potential Records Impacted |
| Conduent5 | February 2026 | 25 million |
|
TransUnion6 |
August 2025 |
4.4 million |
|
Google, Apple, Facebook, etc.7 |
June 2025 |
16 billion |
|
Internet Archive8 |
Oct. 2024 |
31 million |
|
National Public Data9 |
Aug. 2024 |
2.7 billion |
|
Ticketmaster10 |
May 2024 |
560 million |
|
Change Healthcare11 |
Feb. 2024 |
145 million |
|
MOAB (20 brands including Tencent, LinkedIn, X, Venmo, Weibo, Canva, Apollo and Adobe)12 |
Jan. 2024 |
26 billion |
|
23andMe13 |
Oct. 2023 |
4 million |
|
Xfinity14 |
Oct. 2023 |
36 million |
|
Twitter15 |
Jan. 2023 |
200 million |
|
TransUnion16 |
Nov. 2022 |
At least 22 million |
|
Uber17 |
Sept. 2022 |
Unknown |
|
U-Haul18 |
July 2022 |
2.2 million |
|
Apache Log4j19 |
Dec. 2021 |
Everyone |
|
GetHealth (Fitbit and Apple watches)20 |
Sept. 2021 |
61 million |
|
Microsoft Power Apps (Ford Motor Company, American Airlines, government agencies and more)21 |
Aug. 2021 |
38 million |
|
LinkedIn22 |
June 2021 |
700 million |
|
20/20 Eye Care Network23 |
May 2021 |
3 million |
|
OneMoreLead24 |
April 2021 |
126 million |
|
Facebook25 |
April 2021 |
533 million |
|
Reverb26 |
April 2021 |
5.6 million |
|
ParkMobile27 |
March 2021 |
21 million |
|
Compilation of Many Breaches (COMB)28 |
Feb. 2021 |
3.2 billion |
|
SocialArks29 |
Jan. 2021 |
318 million |
|
Neiman Marcus30 |
May 2020 |
4.6 million |
|
Capital One Financial Corporation31 |
July 2019 |
106 million |
|
Under Armour32 |
March 2018 |
150 million |
|
Equifax33 |
Sept. 2017 |
147 million |
*To find more recent breaches, visit the Privacy Rights Clearinghouse.
How Do Data Breaches Happen?
It seems like big-time security measures should be enough to keep cyberattacks at bay, but no safety measure is surefire. Large-scale or minor data breaches can happen anytime a hacker or anyone who isn’t authorized gains access to sensitive files or information. And they happen a lot more often than you might think.
One of the most frustrating things about data breaches is how quickly your data privacy can be undermined by a single weak link. So, who or what is to blame for making these trusted companies vulnerable to data breaches? Anything as minor as a weak password can cause a breach. Like when you’ve used the same password pickles98 for the last 23 years across every single online account you have. Sometimes, though, a website is missing a security patch, or a system glitch is at fault.
In the case of a leak, the company unknowingly triggers the leak of info. This type of incident is also known as an accidental data breach and can be caused by things like failure to follow password guidelines on public-facing web services. We’ve all been there. Whether it’s a new puppy or your personal info, “accidental leaks” are no fun to deal with.
Artificial Intelligence
There’s a new kid on the data breach block: AI. No, not short for Alfred. I’m talking artificial intelligence. In a recent study, 75% of the cybersecurity professionals surveyed reported that they were at least moderately concerned about AI being used in cyberattacks or other harmful activity.34
If you’ve tried any of the free AI tools out there, you might not be too worried (try telling it to draw anything with hands and you get something that looks like a human octopus). But you should know, AI is adept at making top-notch phishing emails without any of the telltale red flags, like grammatical errors, that usually tip humans off.
AI can also be used to scan through loads of stolen data to craft a perfect spear phishing email. It can generate a conversation if someone decides to respond to one of these emails. And it can even clone voices to answer the phone!
But that’s not all. Recently, some criminals after some serious money used AI to deepfake a video call, pretending to be the CFO of a multinational Hong Kong company. They managed to get an employee to transfer $25 million!35 You may not be a multinational billion-dollar company, but that technology could easily be used to steal your data from a large company or worse.
Data breaches don’t seem to be slowing down. A report by Cybersecurity Ventures shows that the global cost of cybercrime is expected to exceed $10 trillion by 2025.36 Which is 10 million millions. Ten thousand billions. Yes, it makes my head hurt too.
Interested in learning more about identity theft?
Sign up to receive helpful guidance and tools.
Types of Data Breaches
By now, we’ve touched on a few different ways data gets breached. But you should know just how creative and clever cyberbaddies can get, so let’s look at even more ways your data can get stolen.
Stolen Information
Believe it or not, people sometimes just straight up steal stuff. A laptop left unattended for a moment, a lost phone, a file sent to the wrong person—all of these are ways for bad people to get their hands on data that doesn’t belong to them. This could include an insider threat—think angry (or just unethical) employees on their way out of a company. In 2022, a research scientist stole 570,000 pages of Yahoo’s intellectual property after he got a job offer somewhere else.37
Malware
This term covers a lot of different things. But basically, malware is software created for bad purposes—like taking over someone else’s device, stealing info, or launching an attack.
Phishing
This isn’t the kind of fishing that involves a tackle box or following the band Phish on their 26-date summer tour. This is where a bad guy creates an email or website that looks legit, then fools the new recruit just trying to get oriented in their new job into sending all their login details to the wrong person. And now that new recruit’s Social Security number is on the dark web. Whoops.
Business Email Compromise (BEC)
This is a form of phishing where the email sent has no attachment or URL you’re supposed to click on. Instead, the criminal crafts the email to feel like it’s from inside your company and often impersonates the CEO, asking you to transfer money or send all the tax info on their employees or something like that.
Ransomware
This one doesn’t involve people being kidnapped for ransom a la Taken (Liam Neeson just let out a deep sigh of relief). This is when a criminal uses malware to lock up a company’s data and hold it for ransom—aka “Send us $2 million or we’ll release all your customers’ sensitive info to the world.” But paying the ransom isn’t a guarantee you’ll get the data back—or that they won’t keep a copy and release it anyway.
This happened to Las Vegas casino operator Caesars. A cybercrime group infiltrated their systems and demanded $30 million in ransom. Caesars eventually agreed to pay $15 million.38
Password Guessing
We’ve all been there—typing in variations of our passwords into the Amazon login until we get it right. Well, cybercriminals do it too. Passwords that are too simple make it easy for bad guys to guess and gain access. An employee leaving a password on a sticky note by their monitor also counts.
What Is Targeted in Data Breaches?
When a hacker makes a cyberattack, they’re usually gunning for any sensitive data they can find—anything that can either be used to steal immediately (like payment information) or get them access to stuff that can be used to steal (like passwords).
Like I mentioned before, sensitive data can include your name, birth date, street address, health care history, customer lists, Social Security number and bank account information. It also includes your zip code, phone number, debit (or credit—boo!) card number, education records or biometric data (think fingerprints to get into your phone).
So, how do these lowlife hackers, who hang out in dark basements with cheese dust on their shirts, plan to get this sensitive data from the interwebs? Through weak credentials (like your password that’s the name of your dog followed by your birth date) or compromised assets (like those leaks we talked about earlier).
Hackers will also target a person or company that has legitimate access to another company’s sensitive data for things like management or maintenance. This is called third-party access. So essentially, you could have the cyber version of the Great Wall of China around your business, but if the little company contracted to do your marketing has one of those dog name/birthday passwords, you’ve got a big gaping hole in your wall.
How Do I Know if I’ve Been Affected by a Data Breach?
If a company experiences a data breach, they’re required by state law to let you know about it.39 It’s news no one wants to hear, but knowing allows you to become hyperalert and keep an eye on things moving forward.
Sometimes, companies even offer compensation—if people sue them. Equifax settled their agreement to make up for the way they handled their 2017 data breach. They handed out compensation for credit monitoring, loss of time and money, and even a partial reimbursement for any monitoring purchased with Equifax.40 If you find out your info is part of a data breach, stay tuned for any lawsuit settlements.
What Can I Do to Protect Myself From Data Breaches?
Here’s the bad news: In this digital age we live in, there’s no way to 100% guarantee you’ll never be part of a data breach. (Unless you become a homesteading recluse who lives off the grid.)
But here’s the good news: It’s not all doom and gloom. And I wouldn’t lose sleep over it. There are plenty of common security practices you can put into place to help protect your data privacy so you are in control.
Shred documents with your personal information listed, never keep your Social Security card in your wallet, and be cautious about who you share your personal information with. Also, be alert and don’t fall prey to all the different types of fraud out there—they’re everywhere, and most of them are pretty easy to spot. Last but not least, don’t forget to arm yourself with identity theft protection.
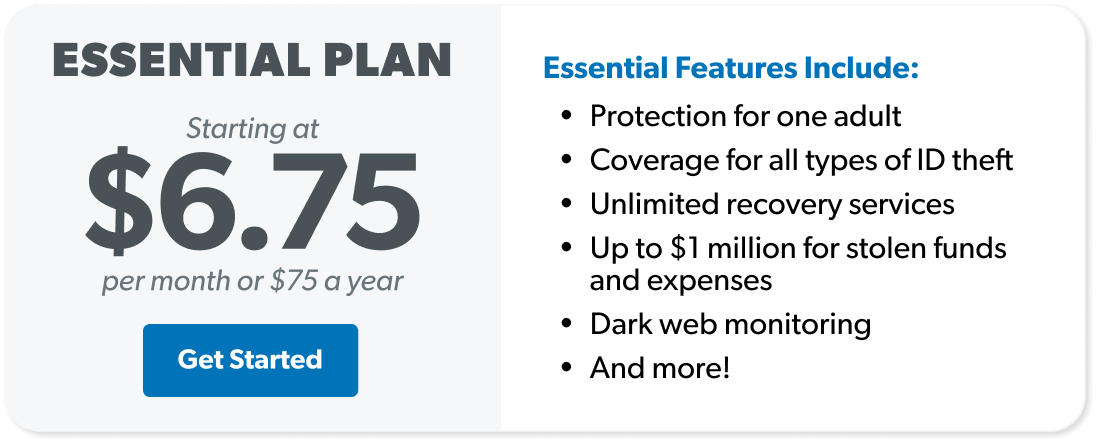
Even if you’ve been given free credit monitoring, when it comes to solid defense, you need to get ID theft protection. It’ll not only protect your information, but more importantly, it’ll help you clean up any messes that come with these awful data breaches.
What Can I Do to Protect Myself From Identity Theft After a Breach?
The best identity theft protection services do more than just sit in the background. They catch fraud fast and send you real-time alerts when something shady pops up. That way, you can shut it down before it spirals out of control. But let’s be clear—not all protection services are created equal.
If a company with your information has a data breach, don’t panic. There are a few smart steps you can take to stay ahead of hackers and prevent identity theft. And remember—a data breach doesn’t automatically mean your identity has been stolen.
Change Your Passwords
It’s a good idea to go ahead and change your passwords—especially if you use the same password in multiple places. Pro tip: Don’t use the same password across accounts! Using the same password for all your social media profiles, email addresses and bank accounts is just asking for trouble. Instead, you should always use unique passwords. I know you think I’m a madman for saying that, but this is the price to pay for digital safety in the modern world.
Creating diverse passwords can be tricky. But whatever you do, don’t rely on a common phrase or anything that’s easy to guess. (Sorry, that means famous quotes and maiden names aren’t good fallbacks.) Get creative!
Let me help you with this:
- Use a combination of uppercase and lowercase letters.
- Use special characters (like ! or # or $).
- Make your passwords long (12 characters minimum).
- Use random words strung together (instead of “merrychristmas” try “GrinchHome@loneElf18”).
Run Security Programs on Your Devices
Hackers are slick. These days, they can break into your phone and grab everything from your emails to your banking info. (Yeah, if your password is sitting in your Notes app . . . it’s time for change.)
The easiest way to prevent someone from hacking your phone is to install and run security software on your device. It’ll flag risky apps, sketchy calls and texts, and it’ll help you clean them out. Good news if you’re an iPhone user—Apple already has built-in malware protection. Android users, you’re covered too: Google’s built-in Protect app helps keep your phone safe, and it won’t cost a dime.
After you’ve kicked the bad stuff off your phone, take things a step further with identity theft protection from Zander, a RamseyTrusted® provider. They’ll monitor your info 24/7 so hackers can’t access your information ever again.
Check Your Credit Report
To be clear, I’m not worried about your credit score here (in fact, I never am). Instead, look through your credit report to see if anything suspicious or odd stands out to you.
You can get one free credit report per year from each of the three major credit-monitoring bureaus. This means you can check your credit report every three to four months. If you can stay on top of your credit report, you could have the upper hand in noticing suspicious activity.
Look for red flags like these:
- Inactive accounts suddenly have activity on them.
- A line of credit appears that you didn’t open.
- Your personal information is incorrect.
- A good standing account is in collections.
- A credit inquiry pops up that you didn’t apply for.
Never ignore red flags! Coincidentally, that advice works for credit reports and even better for relationships.
I know it can be annoying to sift through your bank transactions each day. But then again, if you can make time to scroll through your social media feeds, you should be able to make time to keep your money and identity safe. Need some ice for that burn? But seriously, make time for this stuff!
Your bank should alert you if they see anything irregular going on—but don’t rely on that. It’s much more beneficial if you’re the one checking your account every single day. Because no one cares about your financial safety as much as you.
Get Identity Theft Protection
You can’t have eyes everywhere all at once. A solid identity theft protection program can help keep you from being a sitting duck waiting for identity theft to find you. Be proactive! Make sure you’re prepared before you become a victim of a data breach.
A good identity theft protection program will alert you if anything looks suspicious—like if someone figures out your password. Zander’s ID protection is the same protection I personally use, and it’ll save your butt (and dozens of hours of your precious time) if you get hit by identity theft.
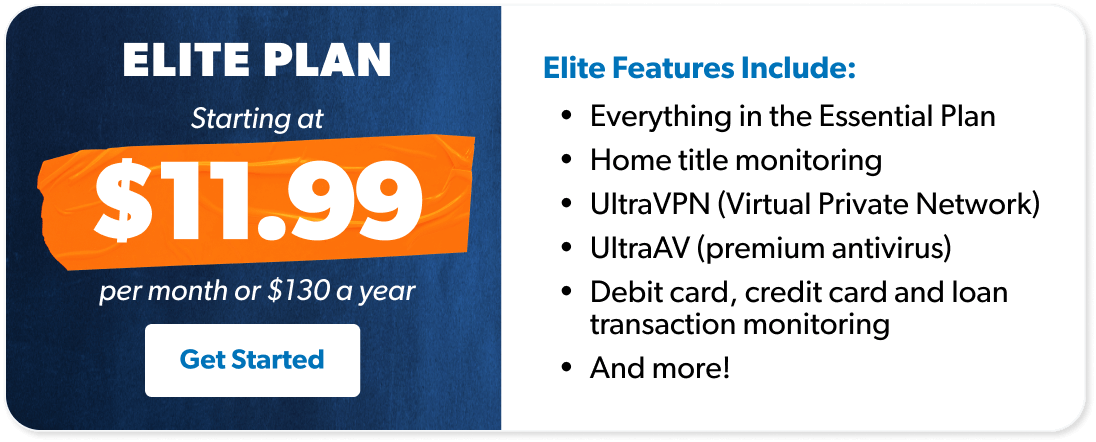
If you want the Chuck Norris of identity theft defense, get Zander’s Elite Bundle. On top of $1 million in restoration coverage, it offers home title monitoring (in case someone wants to pretend your house is theirs), bank and retirement account monitoring, premium antivirus and much more.
Want to protect your data privacy? Get covered with Zander.
Next Steps
- Dig into how to prevent identity theft.
- Learn about what to do if your identity is stolen.
- Get identity theft protection through Zander.

 By
By